All Cybersecurity Courses
Cybersecurity Online Training Courses - Live
Cybersecurity is an ongoing challenge for today’s businesses. With new threats emerging every day, companies need a proactive approach towards identifying potential risks and vulnerabilities. It’s imperative IT professionals have the necessary skills to safeguard their organization against all security breaches. Our vast cybersecurity training portfolio can help you and your team develops cybersecurity skills at every level. We also offer prep courses for top industry-recognized certifications and product-specific courses targeting distinct skills. You and your team learn to approach cybersecurity offensively and defensively through real-world examples and exercises, hands-on labs, and expert instruction. You gain knowledge to close skill gaps, meet and maintain mandates, and sustain and retain a highly qualified workforce. CCS Learning Academy offers CISSP, CHFI, CEH, CCSP, Security +, and many more cybersecurity-related courses.



Filter by Topic
Filter by Vendor
Computer Hacking Forensic Investigator | CHFI
Course Description The Computer Hacking Forensic Investigator (CHFI) course delivers …
What you'll learn
Establish threat intelligence and key learning points to support pro-active profiling and scenario modeling
Perform anti-forensic methods detection
Perform post-intrusion analysis of electronic and digital media to determine the who, where, what, when, and how the intrusion occurred
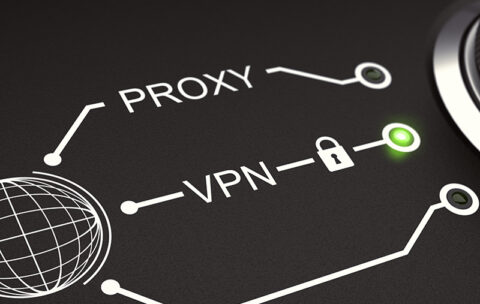
Extract and analyze of logs from various devices like proxy, firewall, IPS, IDS, Desktop, laptop, servers, SIM tool, router, firewall, switches AD server, DHCP logs, Access Control Logs & conclude as part of investigation process.
Identify & check the possible source / incident origin.
Recover deleted files and partitions in Windows, Mac OS X, and Linux
Conduct reverse engineering for known and suspected malware files
Collect data using forensic technology methods in accordance with evidence handling procedures, including collection of hard copy and electronic documents
The computer forensic investigation process and the various legal issues involved
Evidence searching, seizing, and acquisition methodologies in a legal and forensically sound manner
Types of digital evidence, rules of evidence, digital evidence examination process, and electronic crime and digital evidence consideration by crime category
Roles of the first responder, first responder toolkit, securing and evaluating electronic crime scene, conducting preliminary interviews, documenting electronic crime scene, collecting and preserving electronic evidence, packaging and transporting electronic evidence, and reporting the crime scene
Setting up a computer forensics lab and the tools involved in it
Various file systems and how to boot a disk
Gathering volatile and non-volatile information from Windows
Data acquisition and duplication rules
Validation methods and tools required
Recovering deleted files and deleted partitions in Windows, Mac OS X, and Linux
Forensic investigation using AccessData FTK and EnCase
Steganography and its techniques
Steganalysis and image file forensics
Password cracking concepts, tools, and types of password attacks
Investigating password protected files
Types of log capturing, log management, time synchronization, and log capturing tools
Investigating logs, network traffic, wireless attacks, and web attacks
Tracking emails and investigating email crimes
Mobile forensics and mobile forensics software and hardware tools
Writing investigative reports
Dark Web Forensics and IOT Forensics
Certified Ethical Hacker | CEH
This Certified Ethical Hacker Certification is designed to teach students …
What you'll learn
Information security controls, laws, and standards.
Foot printing, foot printing tools, and countermeasures.
Network scanning techniques and scanning countermeasures.
Enumeration techniques and enumeration countermeasures.
Vulnerability analysis to identify security loopholes in the target organization’s network, communication infrastructure, and end systems.
System hacking methodology, steganography, stag analysis attacks, and covering tracks to discover system and network vulnerabilities.
Different types of malware (Trojan, Virus, worms, etc.), system auditing for malware attacks, malware analysis, and countermeasures.
Packet sniffing techniques to discover network vulnerabilities and countermeasures to defend against sniffing.
Social engineering techniques and how to identify theft attacks to audit human-level vulnerabilities and social engineering countermeasures.
DoS/DDoS attack techniques and tools to audit a target and DoS/DDoS countermeasures.
Session hijacking techniques to discover network-level session management, authentication/authorization, and cryptographic weaknesses and countermeasures.
Web Server attacks and a comprehensive attack methodology to audit vulnerabilities in web server infrastructure, and countermeasures.
Web application attacks, comprehensive web application hacking methodology to audit vulnerabilities in web applications, and countermeasures.
SQL injection attack techniques, injection detection tools to detect SQL injection attempts, and countermeasures.
Wireless encryption, wireless hacking methodology, wireless hacking tools, and Wi-Fi security tools.
Mobile platform attack vector, android vulnerability exploitations, and mobile security guidelines and tools.
Firewall, IDS and honeypot evasion techniques, evasion tools and techniques to audit a network perimeter for weaknesses, and countermeasures.
Cloud computing concepts (Container technology, serverless computing), the working of various threats and attacks, and security techniques and tools.
Penetration testing, security audit, vulnerability assessment, and penetration testing roadmap.
Threats to IoT and OT platforms and defending IoT and OT devices.
Cryptography ciphers, Public Key Infrastructure (PKI), cryptography attacks, and cryptanalysis tools.
CSSLP – Certified Secure Software Lifecycle Professional
What Will You Learn From Our CSSLP Training? To become …
What you'll learn
The course on CSSLP teaches how to secure your applications. After having CSSLP certification from (ISC) ², your application security capability within the software development lifecycle will be authorized. In-depth coverage of the eight domains required to pass the CSSLP exam.
Domain 1: Secure Software Concepts
Domain 2: Security Software Requirements
Domain 3: Secure Software Design
Domain 4: Secure Software Implementation/Coding
Domain 5: Secure Software Testing
Domain 6: Software Acceptance
Domain 7: Software Deployment, Operation, Maintenance and Disposal
Domain 8: Supply Chain and Software Acquisition
SSCP – Systems Security Certified Practitioner
Is SSCP A Good Certification Training? Professionals who work with …
What you'll learn
In-depth coverage of the seven domains required to pass the SSCP exam.
Domain 1: Access Control
Domain 2: Security Operations and Administration
Domain 3: Risk Identification, Monitoring, and Analysis
Domain 4: Incident Response and Recovery
Domain 5: Cryptography
Domain 6: Networks and Communications Security
Domain 7: Systems and Application Security
CompTIA PenTest+
Course Description Security remains one of the hottest topics in …
What you'll learn
Plan and scope penetration tests.
Conduct passive reconnaissance.
Perform non-technical tests to gather information.
Conduct active reconnaissance.
Analyze vulnerabilities.
Penetrate networks.
Exploit host-based vulnerabilities.
Test applications.
Complete post-exploit tasks.
Analyze and report pen test results.
CGEIT: Certified in the Governance of Enterprise IT
Course Description By the conclusion of this course, attendees will: …
What you'll learn
Follow the format and structure of the CGEIT Certification Exam
Identify the various topics and technical areas covered by the exam
Enable students to implement strategies, tips, and techniques for taking and passing the exam
Apply key learning to practice questions
CRISC: Certified Risk and Information Systems Control
Course Description This official ISACA Certified in Risk and Information …
What you'll learn
By the end of either the CRISC certification training or CRISC online training course, you will master the four CRISC domains.
Domain 1: IT Risk Identification
Domain 2: IT Risk Assessment
Domain 3: Risk Response and Mitigation
Domain 4: Risk Control, Monitoring, and Reporting
CISM: Certified Information Security Manager
Course Description We offer CISM certification training and a CISM …
What you'll learn
Our CISM certification training and CISM online course provide in-depth coverage of the four domains required to pass the CISM exam.
Domain 1: Information Security Governance
Domain 2: Information Risk Management and Compliance
Domain 3: Information Security Program Development and Management
Domain 4: Information Security Incident Management