Working in IT for the U.S. DoD
February 11, 2021 2023-12-07 17:10Working in IT for the U.S. DoD
Working in IT for the U.S. DoD
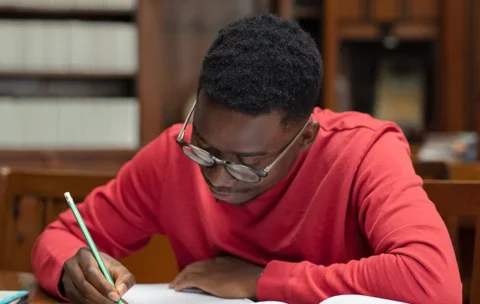
Step into the world of U.S. DoD IT roles. Equip yourself with the knowledge of pivotal DoD Directives and achieve the certifications that set you apart.
DoD Directives 8570, 8570.01-M, and 8140
If you’re interested in working in any technology-related role for the U.S. Department of Defense, you are required per Directive 8140 (which replaced Directive 8570) to obtain and maintain industry certification credentials that have been accredited by the American National Standards Institute (ANSI). This is true for everyone (both civilians and those still serving in the military) who will have privileged access to DoD’s Information Systems.
CCS Learning Academy offers qualified certificate courses from accreditors like CompTIA, (ISC)2, and more! Veterans can work with us to get the credentials they need to be hired for DoD cybersecurity jobs. We can also help individuals obtain the continuing education credits necessary to maintain their existing certifications.

73 %
of workers say that the top benefit of certification is credibility.
57 %
of workers say a certification will help them advance in their current job.
56 %
of workers say a certification will improve their chances for a new position.
In recent CompTIA research, the large majority of IT and business executives involved in security indicated that IT staff certification has made a difference.
CCS Learning Academy
Trusted experts in the technology sector since 1997
IT & business training for professionals at all levels
A network of trainers and clients spanning the entire U.S.
Certifications Approved for DoD Directive 8140/8570.01-M
DoD Directive 8140 is a replacement on and expansion of Directive 8570, which was first released in 2005 to help the DoD manage and audit its cybersecurity personnel. Since then, both the world and technology have changed – a lot! DoD 8140 is the result of several important decisions made to better reflect today’s tech landscape and job market.
Among other updates to DoD 8570, DoD 8140 covers the following:
- Updates and expansions on DoD policies, processes, and responsibilities around managing its cybersecurity workforce.
- The establishment of a DoD cyberspace workforce management council.
- Unification and alignment of technology work roles with regard to baseline qualifications and training requirements.
DoD technology jobs are an excellent fit for many Veterans, as their experiences and clearances translate into distinct advantages in this environment. CCS Learning Academy can help you understand what career pathways are available, what certifications you will need along the way, and how to launch a successful IT career at the U.S. DoD.
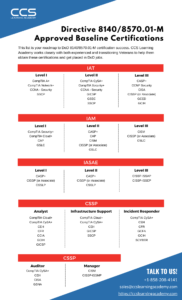
Download this guide to see the complete roadmap to success for aspiring DoD technology professionals per Directive 8140/8570.01-M.
More CompTIA Certifications Now Approved for Directive 8140/8570.01-M!
CompTIA is proud to be the leading choice in certifications for DoD personnel and contractors, helping hundreds of thousands of servicemen, servicewomen, and DoD civilians to meet their Directive 8140/8570 requirements. CompTIA certifications also serve as the building blocks for more advanced certifications; for example, CompTIA Network+ and Security+ are accepted as prerequisites to the Microsoft Software & Systems Academy training course.

CompTIA A+
This credential validates the foundational knowledge for IT Technical Support. It’s recognized as the standard for foundation-level IT knowledge and skills, including installing, configuring, diagnosing and preventive maintenance of hardware and software components, as well as networks and soft skills.

CompTIA Network+
This credential validates the knowledge of networking professionals with at least 9-12 months of experience in network support or administration or adequate academic training. Many corporations recommend or require this certification for their IT employees; it is one of CompTIA’s core certifications.

CompTIA Security+
This credenttial validates mastery of security knowledge for an individual with two years of on-the-job networking experience, with emphasis on security. The exam covers threats, attacks, and vulnerabilities; technologies and tools; architecture and design; identity and access management; risk management; and cryptography and PKI.

CompTIA Cloud+
Approved for three 8140/8570 job roles, this certification validates the expertise needed to maintain and optimize cloud infrastructure services. IT professionals with a Cloud+ certification can better realize the return on investment of cloud infrastructure services. Cloud+ reflects the breadth of skills needed for data center job roles.

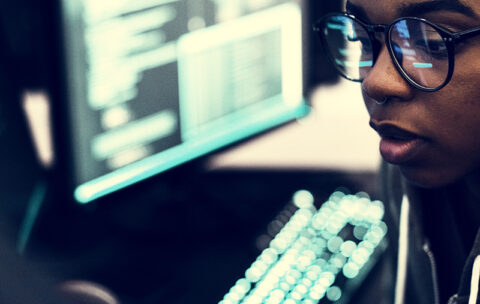
CompTIA CySA+
Approved for five 8140/8570 job roles, this is designed for IT security analysts as well as vulnerability and threat intelligence analysts. The successful candidate has the knowledge and skills required to configure and use threat detection tools, perform data analysis, and interpret the results to identify vulnerabilities, threats, and risks to an organization.

CompTIA CASP+
This certification is designed to meet the growing demand for advanced IT security in the enterprise. It tests critical thinking and judgment across a broad spectrum of security disciplines and requires candidates to implement clear solutions in complex environments. The exam covers enterprise security, risk management and incident response, research and analysis, integration of computing, and communications and business disciplines as well as technical integration of enterprise components.
Why choose CCS Learning Academy?
CCS Learning Academy is one of the industry’s top CompTIA training partners, and we have a team dedicated to working exclusively with transitioning and experienced Veterans. We are honored to assist U.S. service members in transitioning from active duty to high-paying careers in the civilian IT workforce.
Your future is waiting.
Start the next phase of your career today!
Certifications Approved for DoD Directive 8570.01
While DoD Directive 8140 was issued to update and replace DoD 8570, the older Directive 8570 (technically, 8570.01) is still around. It may take a long time to issue a comprehensive manual covering the 8140 security requirements, which is why DoD 8140 still refers to the DoD 8570 manual (“DoD 8570.01-M”).
Like its successor, DoD 8570 requires all users of DoD information systems to meet certain compliance requirements. These requirements include holding certifications accredited by the American National Standards Institute (ANSI). Per the Directive, there are three levels of certification for Information Assurance Technicians (IAT) and Information Assurance Management (IAM) professionals. Anyone wishing to hold these kinds of positions at the U.S. DoD must obtain at least one of the certifications required for the relevant job level.

Download this guide to see the full list of approved baseline certifications per DoD Directive 8570.01.
DoD 8140, 8570.01-M, and 8570-Approved Courses from CCS Learning Academy
CISM: Certified Information Security Manager
What you'll learn
CRISC: Certified Risk and Information Systems Control
What you'll learn
CGEIT: Certified in the Governance of Enterprise IT
What you'll learn
CompTIA PenTest+
What you'll learn
SSCP – Systems Security Certified Practitioner
What you'll learn
CSSLP – Certified Secure Software Lifecycle Professional
What you'll learn
Certified Ethical Hacker | CEH
What you'll learn
Computer Hacking Forensic Investigator | CHFI
What you'll learn
CompTIA Cybersecurity Analyst (CySA+)
What you'll learn
Certified Network Defender | CND
CCAS Check Point Certified Automation Specialist
What you'll learn
CCES Check Point Certified Endpoint Specialist
What you'll learn
CCMS Check Point Certified Multi-Domain Security Management Specialist
What you'll learn
CCSA Check Point Certified Security Administrator
What you'll learn
CCSE Check Point Certified Security Expert
What you'll learn
CCTA Check Point Troubleshooting Administration
What you'll learn
“ To say CCS helped me jumpstart my career is an understatement. CCS helps fresh graduates start their professional journey. They provide comprehensive training both technically and professionally that not only prepares you for a full-time job but also helps make you successful in other aspects of your life.”
– Santosh Gadila
Senior IT Analyst
U.S. Department of Veteran Affairs